Ethereum is much more than just the second largest cryptocurrency in the world. It underpins countless DeFi organisations and is the foundation of the NFT world, paving the way towards a digital art revolution. Despite its significance, there’s always been an unsolved mystery haunting the Ethereum blockchain. Who was responsible for the 2016 attack that stole 5% of all ETH then in existence (equivalent to $11 billion in today’s money and pre-fork)?
The identity of the attacker and the face behind the “DarkDAO” has always been elusive…until now. In a new book, Laura Shin claims to have tracked down and unmasked the culprit. Her findings are fascinating not just as the resolution to an ongoing mystery but because of their wider implications regarding security, traceability and privacy in the cryptocurrency world.
The hack that shook Ethereum
The story has its origins in the fledgling days of Ethereum, in 2016. Back then ETH was a comparatively modest project with very little blockchain activity. Its associated DAO, where members voted on and funded community projects, was popular, though. The DAO was responsible for the biggest crowdfunder in history, raising $139 million.
That’s where things started to go wrong. A mysterious attacker stole 31% of the DAO’s accrued ETH, transferring it in increments to a separate “child DAO” that was eventually nicknamed the “DarkDAO.” Although the hacker now possessed a vast quantity of ETH, rules around the DAO meant that those funds were locked for around a month. This gave the DAO some breathing room and a chance to respond.
Despite some notable resistance, that response took the form of a hard fork. The stolen funds were reclassified as ETC (Ethereum Classic) and worth substantially less than “true” ETH. The fork was supposed to make ETC obsolete but that hasn’t happened. It remains well below the value of ETH but still trades at around $30. The stolen funds are worth roughly $100 million. Although the fork was a partial success, ETC wasn’t completely written off and nor did it seem like the culprit would ever be uncovered.
Pioneering tracking methods
Tracking down the attacker proved difficult because the stolen currency hardly moved. Transactions on the ETC blockchain would have been visible for everybody to see so the hacker was understandably reluctant to make big moves. Some of the currency was converted into Bitcoins but even then the hacker was at pains to disguise their activity. They used Wasabi wallet and a transaction method called CoinJoin, which mixes transactions and makes them nearly impossible to track.
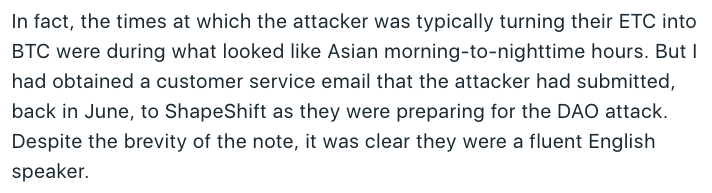
Tracing technology has come on in leaps and bounds since then, though. Analytics firm Chainalysis was able to unpick the transactions and uncover a trail back to the attacker. Shin also undertook her own research. She identified suspects in Switzerland and Russia but they didn’t quite fit the profile. Based on social media interactions and the timings of the Bitcoin conversions, she concluded that the hacker was based in Asia. A customer support email suggested that they were fluent in English.
All the evidence led to one name: Toby Hoenisch, a 36 year old programmer who lived in Singapore when the hack took place but was born in Austria. He's also the CEO and co-founder of TenX, a platform designed to accelerate mainstream crypto adoption by facilitating daily transactions. TenX is notable for the vast sums raised in 2017 ($80 million) to create a crypto debit card. In its heyday, shares in TenX’s token climbed to a market cap of $535 million but have since retreated to just $11 million. There’s still strong interest in the company and its aims, but it’s unclear how (if at all) Hoenisch’s alleged involvement in the Ethereum hack will affect investor confidence.
Mysterious motivations
It should come as no surprise that Hoenisch has flat out denied the allegations. He even claims to have exonerating evidence, although none of this has so far emerged. Given that much of the ETC remains untouched and Hoenisch has business ventures elsewhere, there’s been some speculation about his motivations. Shin suggests that the hack might have been something as simple as a point proving exercise.
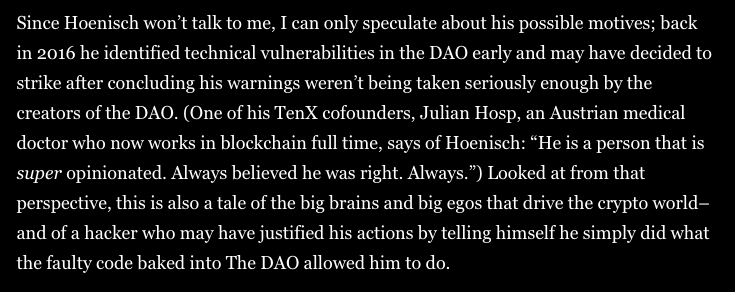
Hoenisch identified security flaws in the DAO but wasn't taken seriously. Shin speculates that this might have motivated the hack, giving the world an insight into what she terms the “big brains and big egos” behind crypto. Just 20 days before the attack he claimed “I’m a white hat hacker by heart.” According to some accounts, Hoenisch is outspoken, to say the least, and likes to be right. Other correspondences including 52 comments in a Slack group about DAO vulnerabilities and an email advising an associate to short ETH are cited as further proof of his involvement.
After the hack, he was vocal on Twitter about his opposition to a hard fork. Moreover, the laundered Bitcoin was traded for Grin (a privacy coin) and then withdrawn to a node called grin.toby.ai. The timings match up perfectly with somebody working in Singapore, and Hoenisch is a fluent English speaker. The evidence certainly appears to correlate. It’s outlined in even more detail in Shin’s new book: The Cryptopians: Idealism, Greed, Lies, and the Making of the First Big Cryptocurrency Craze and her article in Forbes.
Whether Hoenisch is proved beyond all doubt to be the hacker remains to be seen, but this is undoubtedly good news for other victims of crypto theft. Tracking technology is advancing at such a rate that hackers can no longer rely on simply disappearing. While there are some legitimate concerns about privacy, a more secure crypto world inspires confidence and goes some way to undermining the myth that cryptocurrencies are innately unsafe.