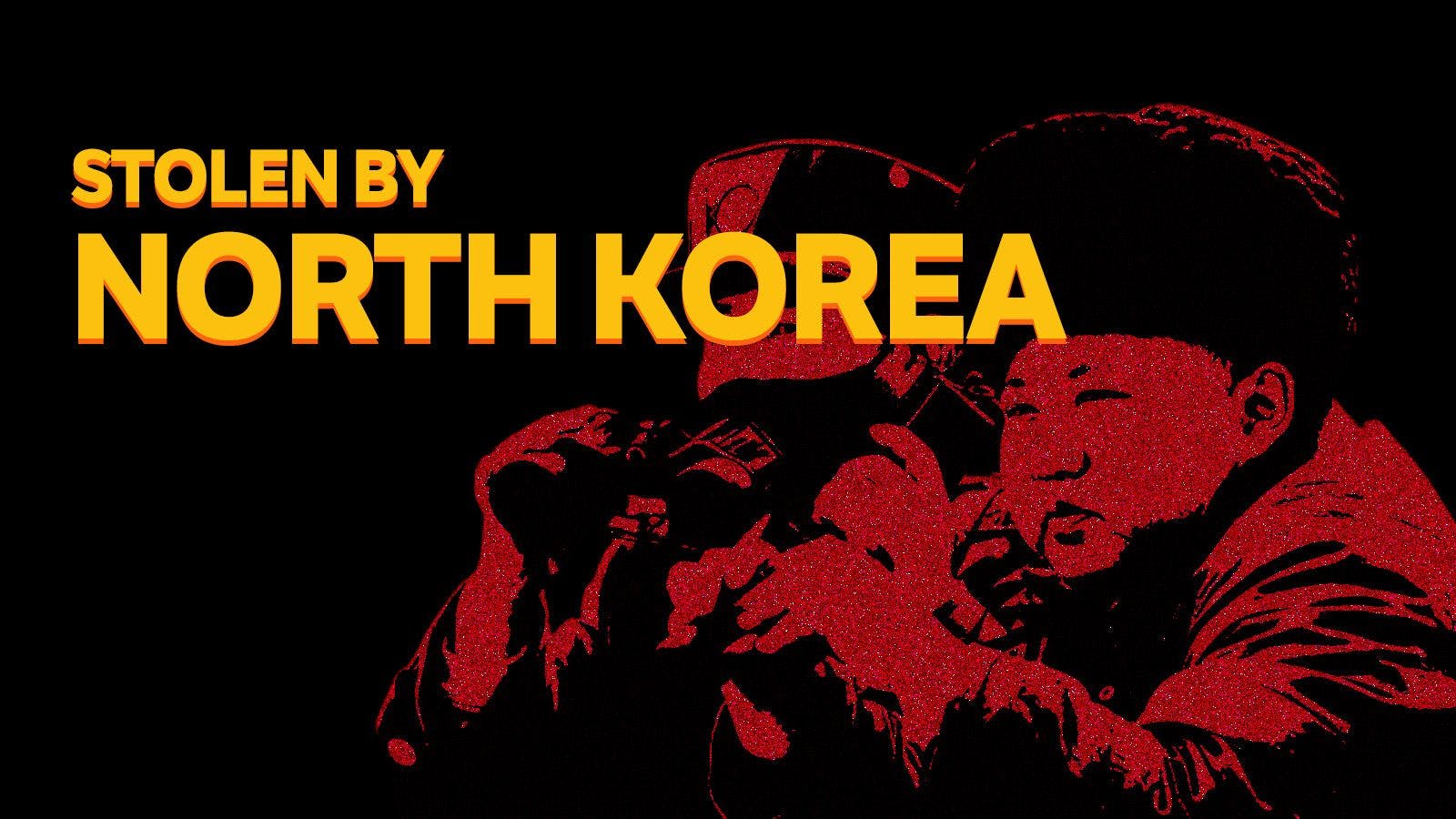
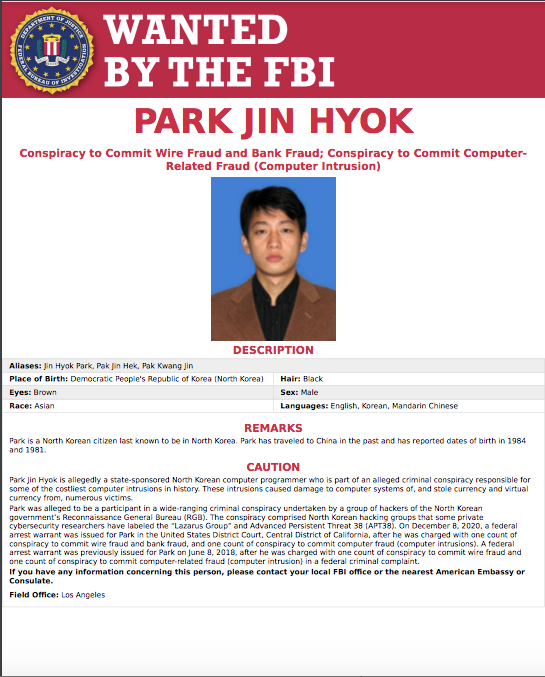
As if the Ronin theft couldn’t get any stranger (after going unnoticed for six days) the FBI has now concluded that the perpetrator was none other than…North Korea. More precisely, the country’s infamous Lazarus Group was behind the theft of $600 million from Ronin Bridge (the ecosystem behind Axie Infinity), the second biggest theft in crypto history. Given that the theft only took place 3 weeks ago, the FBI has moved fast, but they are certain that North Korea is responsible.
An infamous hacking group
Investigations led straight to the APT38 and Lazarus hacking groups. If the latter sounds familiar it’s because they were also behind the 2014 Sony Picture hack, orchestrated in revenge for a film about Kim Jong Un. State backed hacks aren’t unique to North Korea (Russia and China both have high profile cyber units) but the DPRK has always been prolific. The Lazarus Group alone is responsible for the theft of around $1.75 billion.
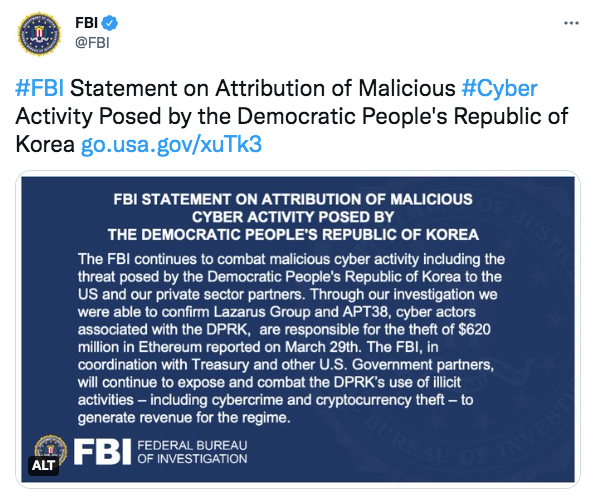
The country’s Bureau 121 trained at least 1000 elite hackers in 2010 while Mirim College is said to develop around 100 new cyber terrorists every year. This kind of state level support gives hackers unprecedented and nearly unlimited resources. As well as software and hardware, training hackers in a centralised manner makes it easier to transfer skills. It also means that they can act with total impunity. Although members of the Lazarus Group are variously sanctioned, monitored and the subject of arrest warrants, there’s nothing anybody can do while they remain on North Korean soil.
The group goes by many different names including Red Dot, Guardians of Peace and Hidden Cobra, all of which appear on a U.S Department of Treasury designation list. North Korean hackers had their most lucrative year yet in 2021, stealing over $400 million in crypto. They’ve already beaten that total in 2022 and it’s only April. Cyber attacks are currently North Korea’s easiest revenue-raising exercise as the country strains under the weight of heavy sanctions. Export and import bans, along with restrictions on financial support, make it difficult for the so-called “hermit kingdom” to generate income.
A lengthy laundering process
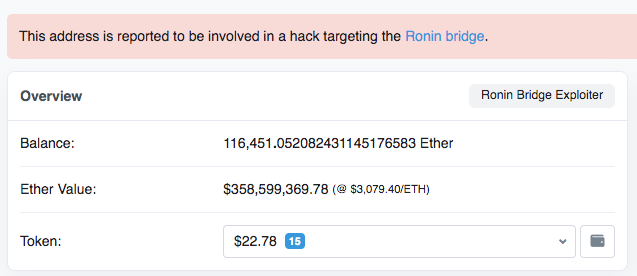
Investigators were able to link profiles, addresses and even hardware used in the theft to the North Korean group. The attackers will now embark on the lengthy process of laundering the money, including via Tornado. Blockchain records show that they’ve been moving vast chunks of ETH through the “mixing” service. The “main” wallet still holds (at time of writing) over $350 million that’s yet to be moved.
Tornado is popular amongst hackers, but software exists that can track even scrambled transactions. Not that the Lazarus Group is likely to face any consequences, though. The threat of extradition is none existent and although most exchanges have now blacklisted any wallets associated with the stolen funds, that’s probably where the consequences end. The state sponsored nature of the theft means that the Lazarus Group is behaving with complete freedom.
For the time being, the offending wallet is labelled “reported to be involved in a hack targeting the Ronin bridge” on Etherscan. This almost certainly won’t be the last that we’ll hear from Lazarus, who also stole millions from ATMs in Asia and Africa using malware and is thought to be behind the dreaded WannaCry ransomware. North Korea’s cyberattack program began as early as the 1990s but now appears to be entering a new phase as the country steps up training.
Was Ronin a soft target?
Axie Infinity likely seemed an easy target for Lazarus. It had scaled back security protocols at the end of 2021 to cope with an influx of new players. Those protocols were supposed to be reinstated but the company forgot, leaving the back door ajar. No Axie tokens were compromised but the lapse was still a serious blow to one of the most popular (and successful) NFT games currently in existence.
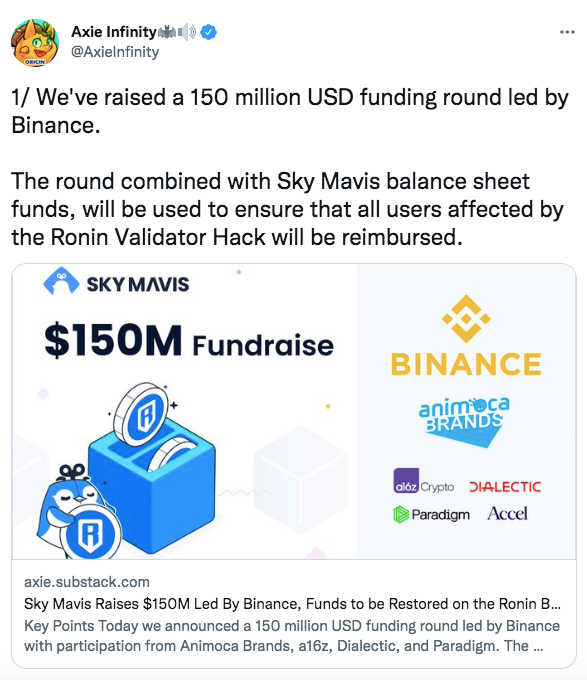
Sky Mavis (the developers behind Ronin Bridge) has since been able to reimburse its users. Binance invested $150 million in the company and other investors including Accel and Paradigm also joined the bailout. The rest of the money will come from reserves. This means that all customers will be repaid and gives Sky Mavis, Ronin and Axie Infinity a chance to focus on the future.
Of course, the developers are working to increase security protocols and safeguard against this kind of attack. The number of validator nodes has been increased and activity across the network is functioning as normal after being briefly frozen. For now, it seems to be business as usual, but with the spectre of state sponsored hacking larger than ever, crypto companies across the world will be on their guard.
Read more:
REVEALED: Is This The Man Behind Ethereum’s Biggest EVER Hack?
Bitcoin Washers Caught in The Act
Hackers Wanted: Dead or Hired